11 | Add to Reading ListSource URL: regmedia.co.uk- Date: 2009-06-03 15:05:53
|
|---|
12 | Add to Reading ListSource URL: www.blackhat.com- Date: 2015-05-28 15:51:25
|
|---|
13 | Add to Reading ListSource URL: www.bromium.com- Date: 2016-12-06 22:44:16
|
|---|
14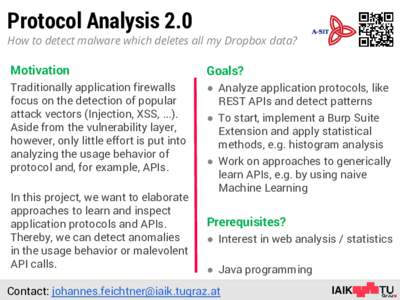 | Add to Reading ListSource URL: www.iaik.tugraz.at- Date: 2015-12-01 06:00:06
|
|---|
15 | Add to Reading ListSource URL: kc.mcafee.com |
|---|
16 | Add to Reading ListSource URL: opensecuritytraining.info- Date: 2015-10-04 21:23:20
|
|---|
17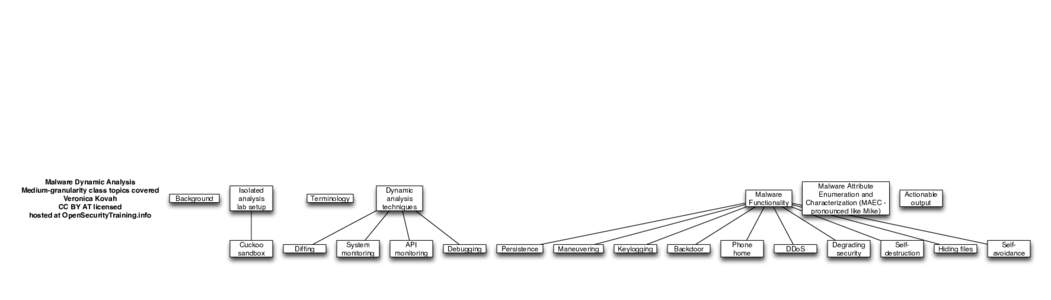 | Add to Reading ListSource URL: opensecuritytraining.info- Date: 2015-10-04 21:23:10
|
|---|
18 | Add to Reading ListSource URL: opensecuritytraining.infoLanguage: English - Date: 2015-10-04 21:23:27
|
|---|
19 | Add to Reading ListSource URL: www.ieee-security.orgLanguage: English - Date: 2015-05-11 16:43:00
|
|---|
20 | Add to Reading ListSource URL: opensecuritytraining.infoLanguage: English - Date: 2015-10-04 21:23:27
|
|---|